
We don’t hangout on the internet anymore. We live on the internet.
Just like our physical world, the internet is a funny place – at it’s times quirky, at times it’s random, and at times it’s safe. Well, we think it’s safe.
As developers and website owners, we are responsible for providing a safe web experience to all of our users.
As users ourselves, we have seen it all –
- Malware injections
- Popups triggering software installs
- Trojan horse viruses
- etc.
Luckily, most of that is over. The modern age browsers take care of these issues by default.
But browsers are just a container that renders whatever the server throws at it. There is only so much it can do. Users (and by extension, websites) are still vulnerable to javascript injections (read more here and here).
Building trust and credibility with users goes a long way. And it is because of this, global leaders such as Mozilla and Google are putting their weight behind making the web a more secure place.
This is contributing to the major reason for a gradual shift from HTTP websites to HTTPS websites.
What is HTTP and what is HTTPS?

Source: https://websitesdepot.com/google-announces-new-security-measure-website-owners-https/
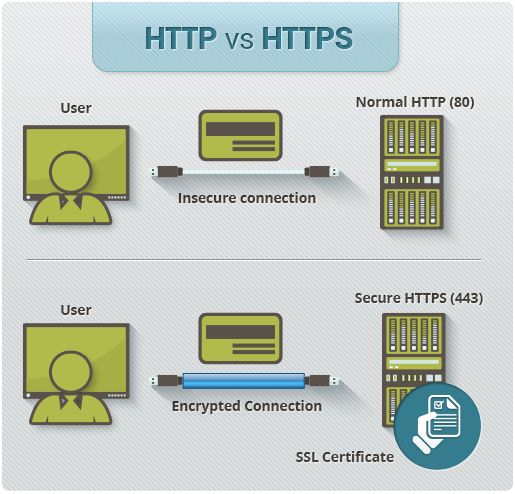
Before we dive deeper, let’s get a quick understanding of HTTP and HTTPS.
These are the most frequently used protocols on the web.
HTTP:
- HyperText Transfer Protocol – a simple protocol for sending and receiving text based messages.
HTTPS:
- HyperText Transfer Protocol Secure – the same protocol as HTTP, but the text is encrypted.
Read this detailed overview to develop a better understanding of HTTP and HTTPS.
How HTTPS bridges the gap:
Google (and many others) are committed to making the web more secure for all the users.
In 2014, Google had their HTTPS everywhere campaign when they announced HTTPS as a ranking signal and started indexing secure pages over unsecured pages.
Google’s indexing conditions:
- It shouldn’t contain insecure dependencies.
- It isn’t blocked from crawling by robots.txt.
- It shouldn’t redirect users to or through an insecure HTTP page.
- It shouldn’t have a rel=”canonical” link to the HTTP page.
- It shouldn’t contain a noindex robots meta tag.
- It shouldn’t have on-host outlinks to HTTP URLs.
- The sitemap lists the HTTPS URL or doesn’t list the HTTP version of the URL.
- The server has a valid TLS certificate.
The first condition is a critical requirement.
The page should not include “insecure dependencies.” Many pages include insecure images, embeds, videos, and so on.
- Google has even created their own guide, “Securing Your Website With HTTPS“.

Source: https://www.keycdn.com/blog/http-to-https/
According to the data from BuiltWith, around only 6.3% of the top 100,000 websites are using SSL.

Apart from the Google ranking boost, there are several other reasons you should consider opting for HTTPS as your website protocol.
Some additional benefits:
- More Security– A major reason why it is important to be running over HTTPS is of course because of security! The reason you need an SSL certificate for e-commerce and other transactional sites is because they are processing sensitive information. For other sites, a big reason for going to HTTPS is the WordPress login page. If you aren’t running over an HTTPS connection, your username and password are sent in clear text over the internet. Anyone can sniff and capture WordPress logins over unsecured connections using a variety of free tools.
- Better Referral Data– Another good reason to migrate is that the referral data is blocked in Google Analytics. If your website is on HTTP and you go viral on any HTTPS website, the referrer data will be completely lost and the traffic from the HTTPS website could end up under “direct traffic” (which is not very helpful). If someone is going from HTTPS to HTTPS, the referrer will still be passed.
- SSL Builds Trust and Credibility– To move to HTTPS, you need an SSL certificate. An SSL certificate builds trust and credibility with your visitors. Visitors tend to look for the green padlock on a website. This gives it “SSL trust”. It is important to let your visitors know you are a secure site and that their information will be safe.
Common myths around migrating to HTTPS

Let’s go ahead and bust these myths.
- My site’s not important enough for HTTPS.
More than often, publishers maintain that their properties don’t handle sensitive user data (login info, payments, etc.) so they can do away with HTTPS.
It is important to note that Javascript-based ad injections are well known to kill user experience.
- Read here about how ISPs including Airtel and MTNL have indulged in such activities.
Moreover, running on HTTP restricts web developers from using key APIs including:
- GeoLocation: You can no longer seek a user’s location if you are on HTTP.
- Web Push Notification: Push notifications are only available on HTTPS.
- GetUserMedia: You can no longer trigger permissions of using a user’s camera/microphone if you are on HTTP.
- HTTP/2: All major browsers support HTTP/2 for HTTPS.
- EME and App Cache: To be removed soon.
- HTTPS will slow down my site.
Quite a few developers have witnessed negative results post migration to HTTPS.
Having said that, when Gmail was migrated to HTTP in 2010, there was no noticeable performance impact.
Here are the stats from the Gmail migration to HTTPS:

Negative results are often because of a lack of optimization such as moving to HTTP/2.
We have to update the way that we talk about HTTPS and performance.
- I can move my site to HTTPS, but what about the 3rd parties I depend on?
Another major concern for publishers is with reference to the third party content on their website – primarily ads [most often the only source of monetization].
A key constraint with HTTPS is that if you move to HTTPS, all of your content (including third party content) also has to be served over HTTPS.
- Note: Google AdSense and Ad Exchange requests are already being served over HTTPS.
There is also the concern about partnerships wherein 3rd party service providers depend on the HTTP referrer header. When a user follows a link from an HTTPS site to an HTTP partner site, browsers will strip their referrer header for privacy reasons.
There’s a web platform feature called “Referrer Policy“ that helps with this.
Publishers can set a referrer policy to allow their partners to see which traffic is coming from their site, but they won’t see the full URL that the user was visiting, so user privacy is maintained.
Then there is a kind of general problem called mixed content.
Mixed content is the problem of loading non-secure HTTP content on HTTPS.
This is important because non-secure sub resources can actually compromise the security of a secure HTTPS site. Browsers will actually block this content and completely wipe out all of the security of that HTTPS site.
Publisher websites (i.e. blogs) contain a lot of old news articles that link to third party images which aren’t available over HTTPS. These images are called passive content and browsers will still allow them to load.
The HTTPS site won’t be completely broken, but that green lock will go away.

Complete video:
This header is basically a way for publishers to assert to the browser that all content should be loaded over HTTPS and that the publishers want to receive reports about any content that isn’t.
Content Security Policy allows publishers to find and fix mixed content across their properties.
Chrome also has a DevTools security panel to make it as easy as possible to find and fix problems with HTTPS configurations such mixed content issues.
Essentially, third party providers must support HTTPS in order for you to fully move your site.
Frequently Asked Questions
- How does this whole communication take place?

When a client/browser requests for a secure session over HTTPS, the server responds with the SSL certificate.
A request is made from the client end and the server responds with the certificate and the server’s public key. The client/browser then checks the validity of the SSL certificate signed by CA. Then the client/browser sends an encrypted session key with the server’s public key. Now the server de-crypts the session key with its private key.
With this, a secure session is created for a secure data transfer.
- How is the data sent over HTTPS secured?
Data sent using HTTPS is secured via Transport Layer Security protocol (TLS), which provides three key layers of protection for your information:
- Encryption – Encrypting the exchanged data to keep it secure from eavesdroppers. The encryption ensures that while browsing, no one can intrude into conversations, track activities across pages, or get access to any information.
- Data integrity – This means data cannot be compromised during transfer and any alteration made to the data cannot be easily detected.
- Authentication – This ensures that users are on the correct website. HTTPS authentication protects against man-in-the-middle attacks and builds user trust.
Here is the full list of frequently asked questions
Getting your SSL certificate
There are numerous options that can be availed to get an SSL certificate while moving from HTTP to HTTPS.
Here are three great options:

| SSLMate issues single-domain certificates for $16/year.
Refer to the guide for installing the certificates and setting up with other common hosts. |

| Let’s Encrypt– Get your absolutely FREE SSL certificate from Let’s Encrypt! You can choose a number of options from their available certificates.
Domain Validation: Single domain or subdomain, no paperwork (just email validation), cheap, issued within minutes. Business/Organization Requires business verification and provides a high level of security, issued within 1-3 days. Extended Validation: Requires business verification which provides a higher level of security, issued within 2-7 days. You can check the Full Documentation and get your SSL certificate from https://letsencrypt.org/ |

| AWS Certificate Manager (ACM). These certificates are free and issued directly by Amazon and last a little over a year. However, they currently require manual issuance through email validation, and do not support Certificate Transparency. Here’s a good ACM guide for Jekyll. |
Things to do while making the switch

First of all, buy and activate an SSL certificate if you haven’t already.
During the migration, there could be some hurdles stalling the process.
Errors may occur when Google starts crawling the HTTP version of your website and generating content duplication issues, with both HTTPS and HTTP versions of the pages shown and different versions of the page showing on HTTP and HTTPS.

Check out these other common pitfalls in using HTTPS/TLS.
Best practices when migrating to HTTPS:

- Using robust security certificates. As part of enabling HTTPS for your website, you must obtain a security certificate (SSL certificate). The certificate is issued by a certificate authority (CA) which takes steps to verify that your web address actually belongs to your organization. While setting up your certificate, ensure a high level of security by choosing a 2048-bit key. If you already have a certificate with a weaker key (1024-bit), an upgrade would be a great way to go.
- Redirect your users and search engines to the HTTPS page or resource with server-side 301 HTTP redirects.
- Use a web server that supports HTTP Strict Transport Security (HSTS) and make sure that it’s enabled.
The idea behind the whole HTTP to HTTPS switch is to provide a safer web experience, ensuring your personal information stays private and does not get misused.
Anything and everything could be personal to you or your end users.
Even if you are searching for “Nexus 5 cost in India”, that search could be private to you. Whether you are browsing or looking for a product or reading an article, you generally do not want what you’re doing to be public information. Particularly for personal information, banks, and transaction information, HTTPS has become a necessity and an industry standard.
Though HTTPS migration is highly recommended and being followed by most website developers, the final decision depends on you. For those who are ready to follow this safer web practice, get started with HTTPS by grabbing your SSL certificate and be delighted to have that green padlock on your website.
Have you made the switch to HTTPS? Let me know in the comments below.


![15+ Best Link Building Tools For Hyper Growth [2026 Reviews]](https://www.shoutmeloud.com/wp-content/uploads/2023/12/Best-Link-Building-Tools-431x230.webp)


Great article, one things still i can’t get answer that my blog opens on both “http” and on “https”. i am afraid whether there may have duplicate content issue or not? if it does how to get rid of it? please i want to know about it. because i didn’t paid for “https” certificate till now. i am novice in terms of blogging too, so i prefer to save bit money and want to attach with “http”. What tricks will be best for me to be safe from duplicate content issue in this scenario?
@John
You need to take immediate action. That would create the duplicate content issue. HTTP version should redirect automatically (301 permaredirect) to HTTPS version. These days you can use free SSL certificate from Cloudflare or LetsEncrypt.
If you are using Bluehost hosting, they also offering free SSL. Here is the guide that would help you: https://www.shoutmeloud.com/free-ssl-certificate-bluehost-hosting.html
Hi Ruchika,
thanks for sharing a great article. still i have 2 queries for you. the first one is after redirecting http to https (301 redirect), do we still need to verify http form in google console (also the sitemaps with http? ) , and do we need to verify https form in Google console. second thing , i will be having a robots.txt file of http:mywebsite.com, do i need to change it to https in robots file?